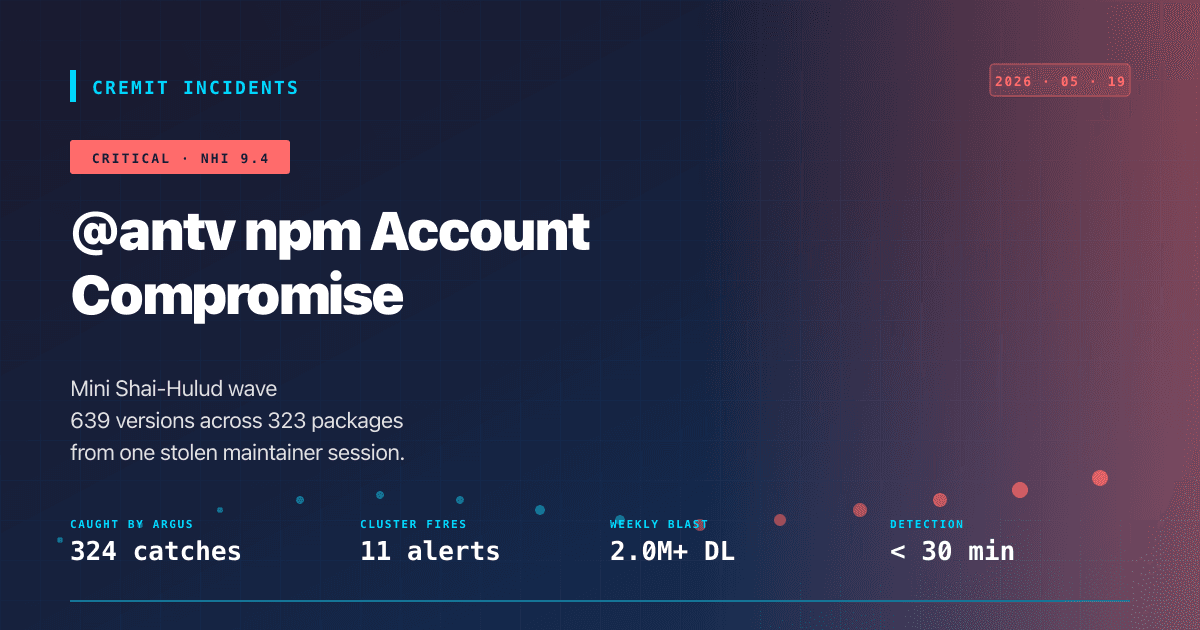
AntV npm Compromise: How Cremit's Argus Pipeline Surfaced 324 Mini Shai-Hulud Catches Within 30 Minutes
Between 01:39 and 02:56 UTC on May 19, 2026, two tight publish bursts placed 639 malicious versions across 323 packages on npm. The single stolen `atool` session was only the entry point — the payload's worm logic harvested every additional maintainer npm token on the infected host and republished under those identities, which is why the wave spans 30 publisher handles. Cremit Argus surfaced 324 catches within thirty minutes via an OSV-MAL override path that intentionally bypasses LLM agreement for OSSF-flagged events. This article documents the attack structure, the detection methodology, and the false-positive trap that nearly slipped past during initial analysis.